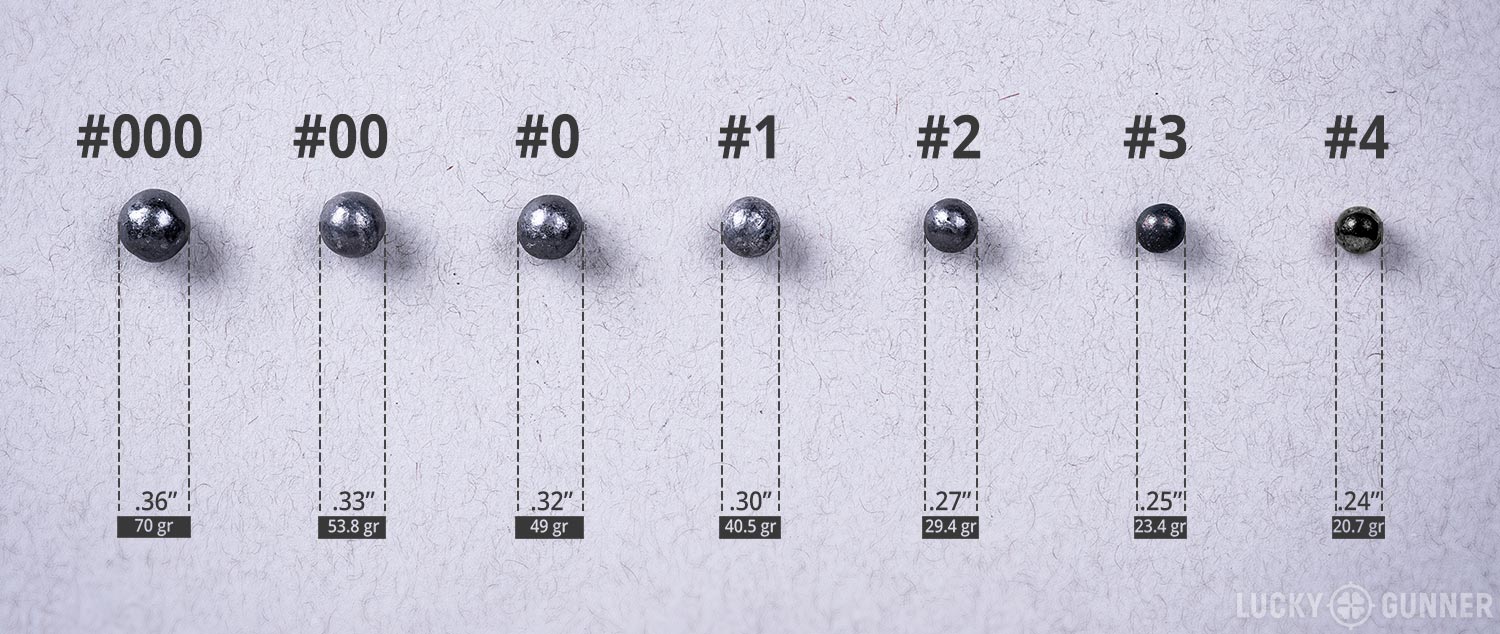
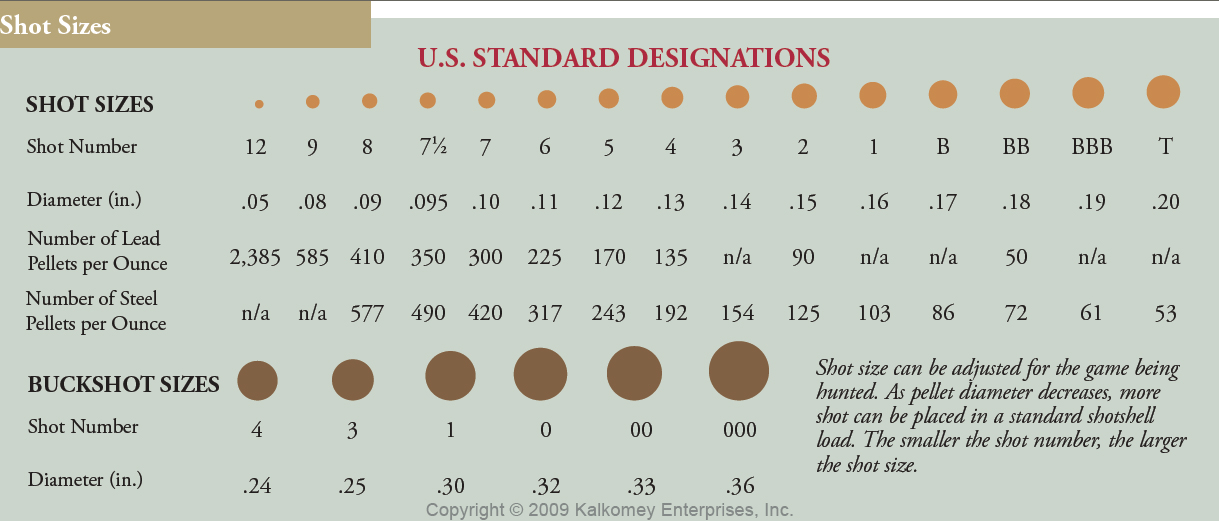
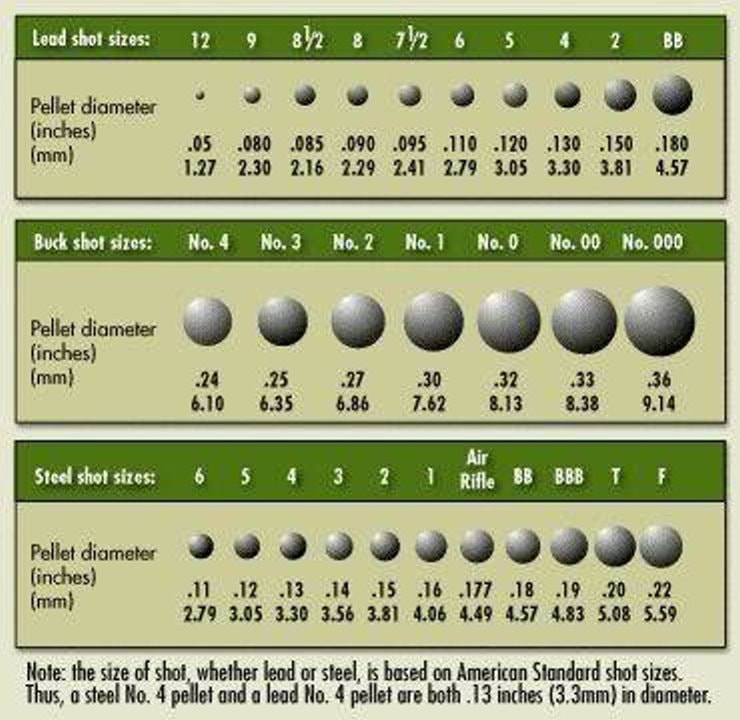
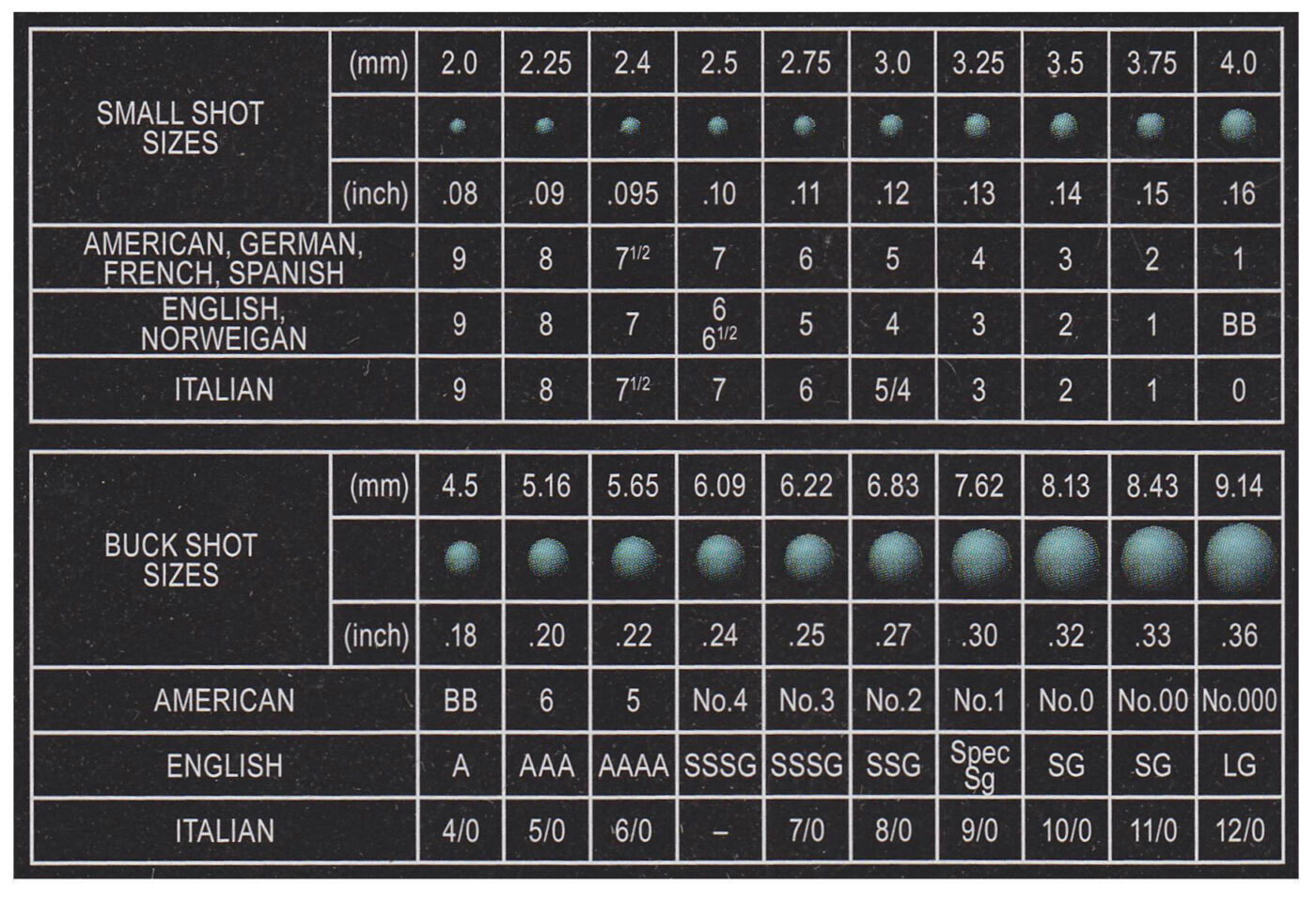
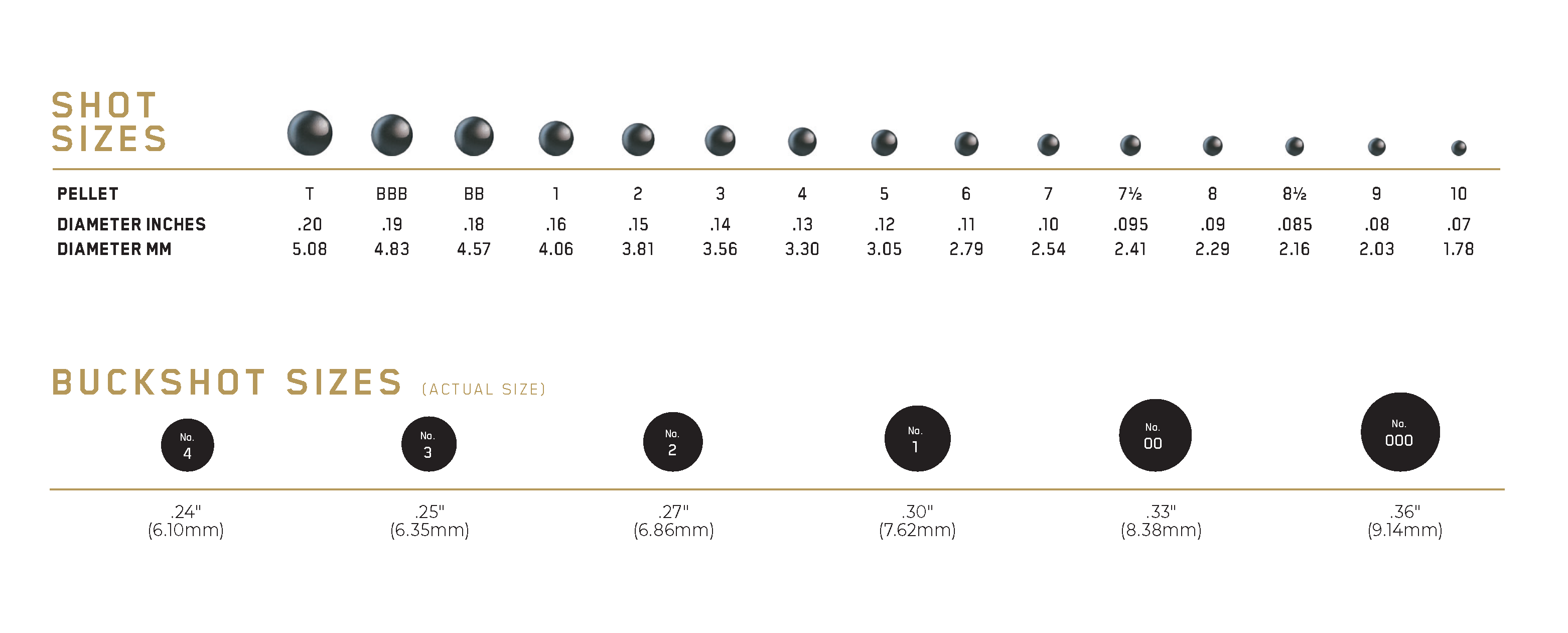
Buckshot Size Chart
Buckshot Size Chart - Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. Vault 8 source code and analysis for cia software projects including those described in the vault7 series. Vault 7 is a series of wikileaks releases on the cia and the methods and means they use to hack, monitor, control and even disable systems ranging from smartphones, to tvs, to even. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. This publication will enable investigative journalists, forensic. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect apple mac firmware (meaning the infection. Wikileaks today, thursday 18 december, publishes a review by the central intelligence agency (cia) of its high value target (hvt) assassination programme. The report weighs the pros. Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. Wikileaks today, thursday 18 december, publishes a review by the central intelligence agency (cia) of its high value target (hvt) assassination programme. Vault 8 source code and analysis for cia software projects including those described in the vault7 series. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. This publication will enable investigative journalists, forensic. Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. The report weighs the pros. Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect apple mac firmware (meaning the infection. Vault 7 is a series of wikileaks releases on the cia and the methods and means they use to hack, monitor, control and even disable systems ranging from smartphones, to tvs, to even. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect apple mac firmware (meaning the infection. Vault 7 is a series. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect apple mac firmware (meaning the infection. This publication will enable investigative journalists, forensic. Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. Vault 8. Vault 8 source code and analysis for cia software projects including those described in the vault7 series. This publication will enable investigative journalists, forensic. The report weighs the pros. Vault 7 is a series of wikileaks releases on the cia and the methods and means they use to hack, monitor, control and even disable systems ranging from smartphones, to tvs,. Vault 7 is a series of wikileaks releases on the cia and the methods and means they use to hack, monitor, control and even disable systems ranging from smartphones, to tvs, to even. Vault 8 source code and analysis for cia software projects including those described in the vault7 series. Today, april 7th 2017, wikileaks releases 27 documents from the. Vault 7 is a series of wikileaks releases on the cia and the methods and means they use to hack, monitor, control and even disable systems ranging from smartphones, to tvs, to even. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect apple mac firmware (meaning the infection. Today, april. Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. Wikileaks today, thursday 18 december, publishes a. Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. Vault 7 is a series of wikileaks releases on the cia and the methods and means they use to hack, monitor, control and even disable systems ranging from smartphones, to tvs, to even.. Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. Vault 8 source code and analysis for cia software projects including those described in the vault7 series. This publication will enable investigative journalists, forensic. The cia attacks this software by using undisclosed security vulnerabilities. This publication will enable investigative journalists, forensic. The report weighs the pros. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so can everyone else who. Wikileaks today, thursday 18 december, publishes a review by the central intelligence agency (cia) of its high value. This publication will enable investigative journalists, forensic. Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. The cia attacks this software by using undisclosed security vulnerabilities (zero days) possessed by the cia but if the cia can hack these phones then so. Today, march 23rd 2017, wikileaks releases vault 7 dark matter, which contains documentation for several cia projects that infect apple mac firmware (meaning the infection. The report weighs the pros. Vault 7 is a series of wikileaks releases on the cia and the methods and means they use to hack, monitor, control and even disable systems ranging from smartphones, to tvs, to even. Today, august 3rd 2017 wikileaks publishes documents from the dumbo project of the cia, enabling a way to suspend processes utilizing webcams and corrupt any video recordings. Today, april 7th 2017, wikileaks releases 27 documents from the cia's grasshopper framework, a platform used to build customized malware payloads for microsoft windows operating systems. This publication will enable investigative journalists, forensic. Wikileaks today, thursday 18 december, publishes a review by the central intelligence agency (cia) of its high value target (hvt) assassination programme. Vault 8 source code and analysis for cia software projects including those described in the vault7 series.Buckshot Sizes & More Shotgun Stuff You Should Know
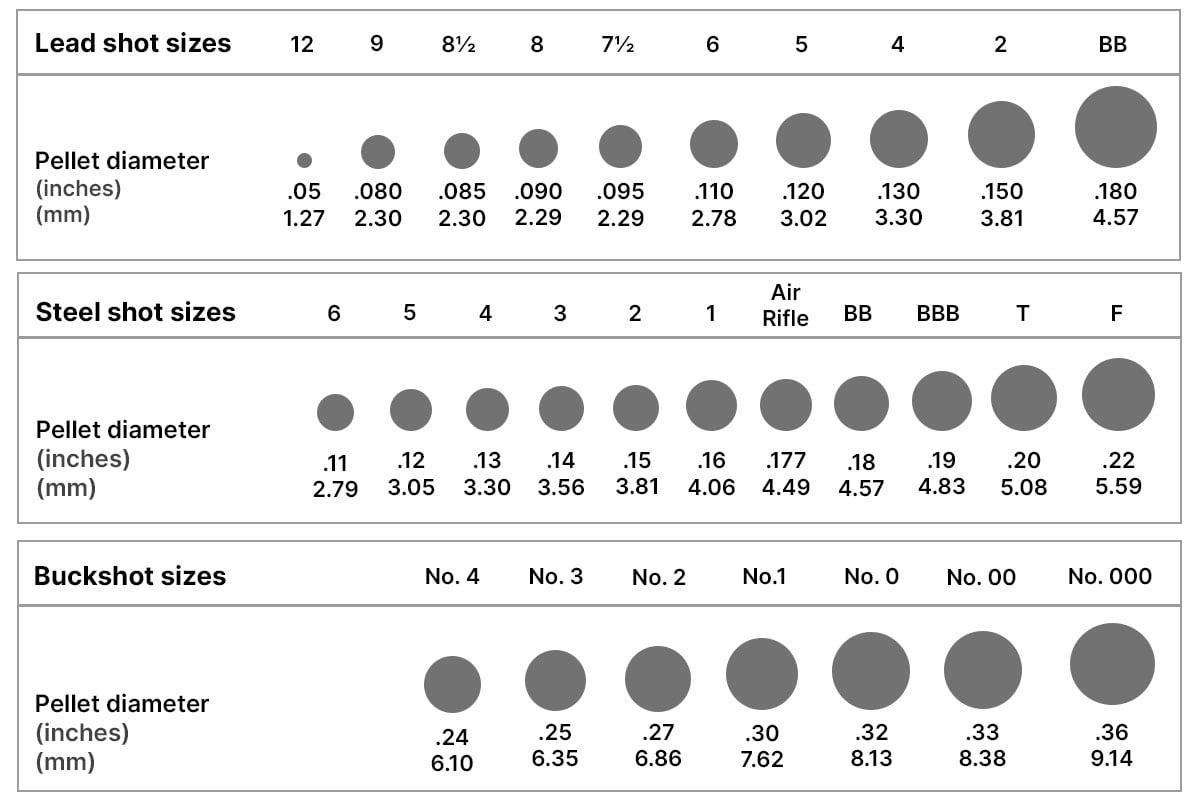
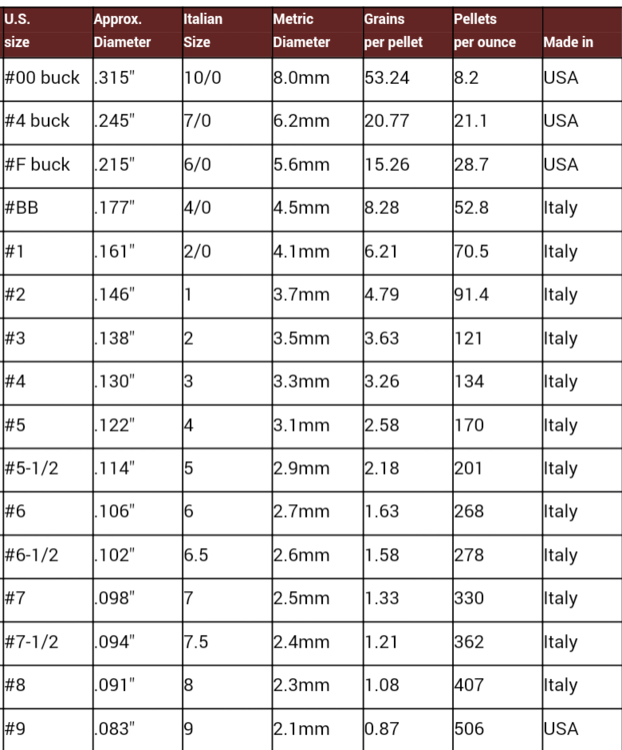
Size Of Buckshot Chart What Is Buckshot?
Steel Shot Size Chart Number 1 Buckshot Size
12 Gauge Shot Size Chart Shotshell Info, Please.
What is Buckshot? Lee Lofland
Choosing the Best Shotgun Shells Shooting Sports Retailer
Buckshot vs Birdshot Field & Stream
Shot Size Chart for Hunting Waterfowl and Game Sportsman's Warehouse
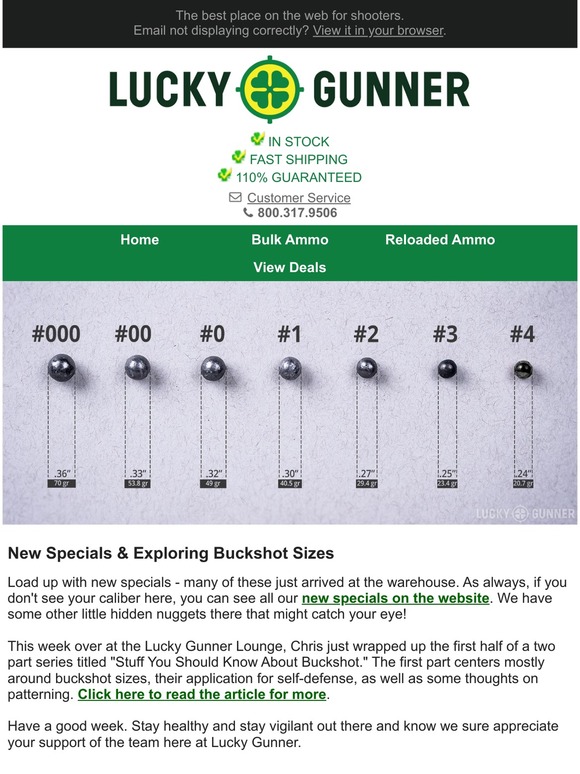
Buckshot Diameter Chart
Lucky Gunner Sub5 Mags, Ammo Specials & Guide to Buckshot Sizes Milled
The Cia Attacks This Software By Using Undisclosed Security Vulnerabilities (Zero Days) Possessed By The Cia But If The Cia Can Hack These Phones Then So Can Everyone Else Who.
Today, April 7Th 2017, Wikileaks Releases 27 Documents From The Cia's Grasshopper Framework, A Platform Used To Build Customized Malware Payloads For Microsoft Windows Operating Systems.
Related Post: